Cyber Mercenaries: The State, Hackers, and Power by Tim Maurer
Cambridge University Press, Jan. 2018, Paperback 266pp $29.99USD
ISBN-10:Â 110756686X | ISBN-13:Â 978-1107566866
Cyber Mercenaries: publisher’s website link
Available online and from all good bookshops.
Tim Maurer confessed in a recent interview that the title of his book was not the one he originally intended to use. Rather, the title was mandated by the marketing department of his publisher, wherein it was thought that “mercenaries†sounded sexier than “proxies†[1].
Such titular shenanigans are commonplace in publishing—journalists often complain that headline writers trivialize their reporting—but in this case it was acceptable shorthand to attract the attention of the potential audience. Importantly, the differences between the actors and activities that the two words represent is the key to the substance of the book.
The author co-directs the Cyber Policy Initiative at the Carnegie Endowment for International Peace and co-chaired the Advisory Board of the 2015 Global Conference on CyberSpace. His book is in keeping with that serious and specific background. The text is not a journalistic romp through breathless narratives involving nerdy cyber warriors engaged in black-hat and white-hat duels.
Readers who want a deeper understanding of how cyber activity is conducted will be well-served by Cyber Mercenaries. The possession of a vocabulary of terms and an understanding of the dynamics of the phenomena are a good place to start for an awareness of the nuances in the words and phrases that are bandied about in the media, such as “state-sponsored hacking†and “cybercrimeâ€. Maurer provides an instructional analysis of the different relationships between cyber actors, how those relationships frequently change and evolve, and what the significant impacts may be. He provides a framework for modeling and understanding those relationships and activities.
 Tim Maurer (R) on Cyber Mercenaries at a Lawfare Hoover Book Soirée
Tim Maurer (R) on Cyber Mercenaries at a Lawfare Hoover Book Soirée
with Lawfare Editor-in-Chief Benjamin Wittes (L)
Throughout Cyber Mercenaries, Maurer is careful to give definitions of the terms he uses. Part I Section 2 (Framework for Thinking About Proxies) opens with this definition: “…a proxy actor can be defined as an intermediary that conducts or directly contributes to an offensive action that is enabled knowingly, actively or passively, by a beneficiary.†The author takes more than half a page in the endnotes to expand upon this definition. One small criticism is that no guidance is offered as to which notes are merely supportive references and which contain extra information. Checking every endnote is as distractive as footnotes would be.
A reference list of abbreviations is included at the front of the book, but not a glossary of terms used in the text. A typology is a classification by type; the historical antecedents of proxies—such as mercenaries, privateers, and buccaneers—are discussed with more modern terms such as orchestrators and sponsors. The Yahoo! data breach example [2] from the Lawfare Podcast gives a portrait-in-miniature of some of the different types of hackers, and importantly how a hacker can at one and the same time be both a state proxy and a cyber criminal in much the same way that swashbuckling privateers of the past operated.
The first part of Cyber Mercenaries (Of Brokers and Proxies) is a finely grained typology of the various kinds of cyber proxies and the cyber activities that the parties undertake. The second part (Cyber Proxies Up Close) contains examination of some specific sovereign states and their use of proxies. The third part (Implications) draws together the ways in which the activities of a range of sponsors and proxies interact, and what consequences the processes and outcomes of those relationships have manifested and might entail. There is a short concluding section that discuses the future, with suggestions for further research.
The writing is fluent, and lighter than might be expected in a work of deep scholarship, although the detailed nature of the discussion makes demands upon the reader’s focus and attention span. The final part of the book is an exhaustive list of sources, which thankfully do not appear as footnotes, but as an appendix. Equally thankfully, that appendix is a rich resource for fact checking and further reading. The overall result of the author’s scholarship is both compelling and enlightening.
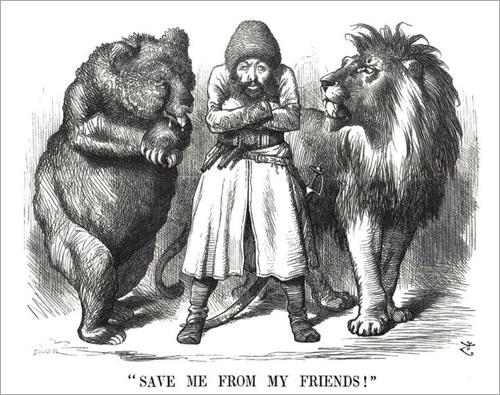 Great Game cartoon from 1878 (Wikimedia Commons)
Great Game cartoon from 1878 (Wikimedia Commons)
It is easy to be blasé about cyber interference, in the same way that the epithet The Great Game made light of the serious rivalry between the British and Russian empires in the nineteenth century; the deeper issues of both of these conflicts continues to impact everyone on both sides. A wider public understanding of cyberspace issues and activities has to be a good thing for the national and international democratic discourse, and valuable knowledge for voters to be armed with as they approach the ballot box. Mercifully, the book does not stray into contentious political messaging, avoiding the incessant background noise of tribal invective that plays out daily in the media.
The USA has mid-term elections later in 2018, which present a further opportunity for the interference experienced in the 2016 US elections. Admiral Michael S. Rodgers, Director of the National Security Agency, Commander of USCYBERCOM (the US Cyber Command, which was elevated to the status of a Unified Combatant Command by President Trump on 17 Aug. 2017), and Chief of the Central Security Service until his scheduled retirement on 04 May 2018, testified before the US Senate Armed Services Committee on 27 Feb. 2018, “Clearly what we have done hasn’t been enough.â€
 Admiral Michael S. Rodgers: clipped from C-Span.org video coverage
Admiral Michael S. Rodgers: clipped from C-Span.org video coverage
We have provided links to freely accessible resources that might tempt you into exploring the subject further. Cyber Mercenaries is recommended for readers prepared to invest some time and effort into understanding how geopolitics and conflict have shifted into a different domain with different actors, tactics, strategies, and outcomes. This is not a text suitable for casual reading; your effort and attention will be amply rewarded. The subject is something we should all care about enough to make the time to engage with more deeply than most of us do now.
[1] Timestamped 02:00Â Lawfare Podcast 10 Apr. 2018 audio excerpt
[2] Timestamped 04:05Â Lawfare Podcast 10 Apr. 2018 audio excerpt
The Lawfare Podcast 10 Apr. 2018 with Tim Maurer on Cyber Mercenaries
A Hoover Hoover Book Soirée with Lawfare Editor-in-Chief Benjamin Wittes
YouTube audio-visual version of the Lawfare interview
Here’s how hostile states are hiding behind ‘independent’ hackers
Washington Post article by Tim Maurer
Why the Russian Government Turns a Blind Eye to Cybercriminals
Slate Future Tense article by Tim Maurer
Leave a Reply
You must be logged in to post a comment.